Security is often introduced in academic courses as a necessary technical requirement, usually explained through models, definitions, and examination-focused notes. However, when one looks closely at how everyday digital systems operate—such as college ERP portals, online banking platforms, or e-commerce websites—it becomes clear that security is not an optional layer. It quietly governs every interaction that takes place within an application.
This document is written as an academic reflection rather than a technical guide. The intention is to present authentication and authorization as design ideas that students regularly encounter across BCA and MCA subjects, and to conceptually relate these ideas to the way modern frameworks such as Spring Boot approach application security.
1. Understanding Security Beyond Theory
In classroom learning, security concepts are often introduced through structured explanations and diagrams. While this approach helps build vocabulary, it may not immediately convey why security decisions influence almost every part of a system. Applications today interact continuously with users, services, and external platforms, making security an ongoing concern rather than a one-time configuration.
From a software engineering viewpoint, security is closely tied to trust. A system must be confident about who is interacting with it and must consistently enforce boundaries. This perspective aligns well with discussions on system responsibility and reliability found in Software Engineering and System Design subjects.
2. Authentication as an Identity Check
Authentication is commonly associated with login screens, but limiting it to that view oversimplifies its role. At its core, authentication is a process of identity confirmation that mirrors real-world practices, such as verifying identity before granting access to restricted spaces.
In academic subjects like Computer Networks, Web Technologies, and Cyber Security, authentication appears in discussions about secure communication and data protection. When students relate these ideas to real applications, authentication emerges as a continuous validation process rather than a single step.
3. Authorization as Controlled Access
Once a user’s identity is verified, the system must decide what actions are permitted. Authorization defines these limits. This concept is familiar in academic environments, where different users share the same platform but operate under distinct privileges.
Role-based access control, discussed in Information Security and Distributed Systems, offers a structured way to manage authorization. Instead of assigning permissions individually, roles simplify decision-making while maintaining system control.
4. Relating These Concepts to Spring Boot
Spring Boot is widely adopted in industry because it provides structured solutions to recurring application challenges. Security is one such challenge. By integrating Spring Security, the framework promotes a standardized approach to authentication and authorization.
For students studying Advanced Java or Enterprise Application Development, this framework-based approach demonstrates how theoretical models discussed in class are translated into reusable, maintainable components in real systems.
5. Authentication Flow in Spring Security (Conceptual View)
Understanding how Spring Security processes authentication internally helps clarify how frameworks enforce security rules. The diagram below represents the conceptual flow involved when a user attempts to access a secured application.
Implementing Authentication and Authorization Using Spring Boot
Below is a simple and academic-friendly example using Spring Security with in-memory authentication.
Step 1: Add Required Dependencies (pom.xml)
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-security</artifactId>
</dependency>
Step 2: Security Configuration Class extends web security configuration adapter
Step 3: Controller with Role-Based Access using ant matcher /request matcher ()
How This Example Demonstrates Authentication and Authorization
- Authentication:
Users log in using username and password (student,admin) - Authorization:
/student/home→ only STUDENT role
/admin/home→ only ADMIN role
This clearly separates identity verification and access control.
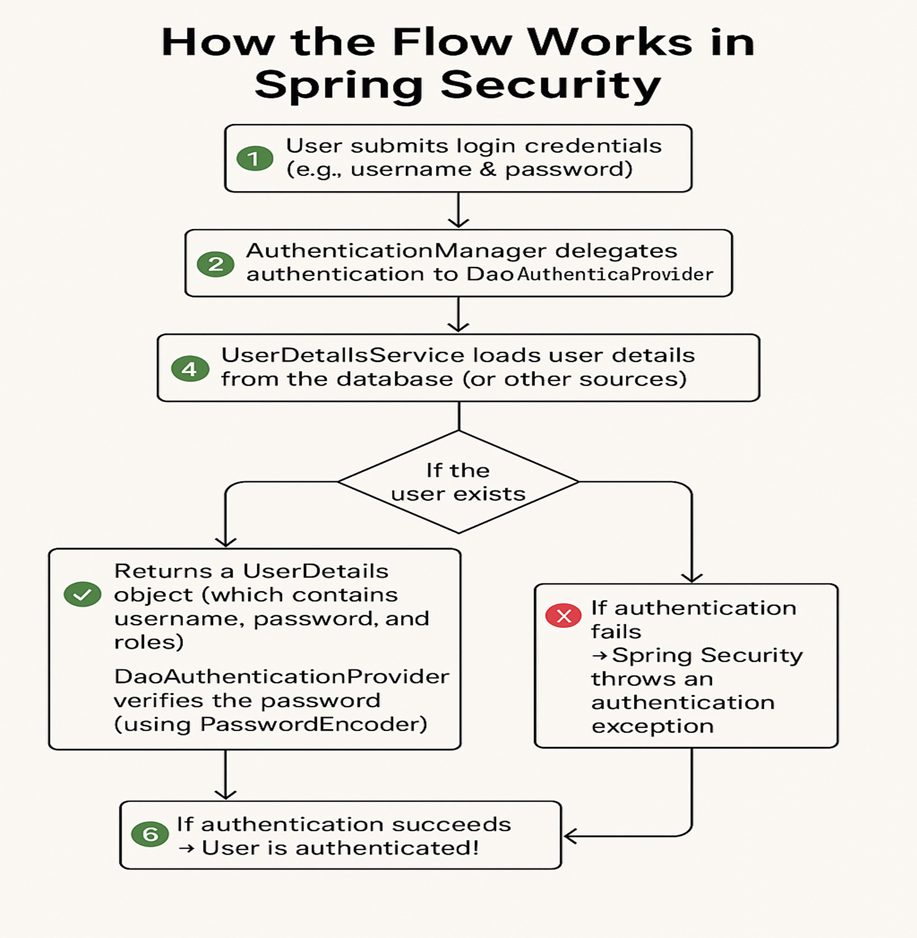
When credentials are submitted, they are handled through multiple layers. An authentication manager coordinates the process, delegating validation to providers and services. User details are retrieved, passwords are verified, and outcomes are decided based on predefined rules.
This layered design closely resembles middleware processing concepts discussed in Web Technologies and Distributed Systems, where responsibility is intentionally divided to improve reliability and clarity.
When simple Spring Boot examples are observed in academic contexts, they often demonstrate in-memory users and role-based access. While these examples are intentionally minimal, they clearly separate identity verification from access control, helping learners see the distinction between authentication and authorization.
6. Academic Mapping to BCA and MCA Curriculum
At the BCA level, students encounter authentication and authorization concepts across multiple subjects, including Computer Networks, DBMS, Web Technology, and introductory Cyber Security courses. These subjects collectively establish the foundation needed to understand secure system behavior.
In MCA programs, the same ideas are revisited with greater depth through Advanced Java Programming, Cloud Computing, Distributed Systems, and Information Security. The emphasis gradually shifts from understanding concepts to applying them architecturally.
7. Why Reflective Understanding Matters for Students
Relying solely on configuration examples may support short-term learning goals, but reflective understanding supports long-term system design skills. When learners understand why security mechanisms exist, they are better prepared to make responsible design decisions.
This approach also encourages questioning and reasoning, which are essential qualities for developing robust and ethical software systems.
8. Conclusion
Authentication and authorization are not isolated technical features. They represent foundational design principles that shape how users interact with applications. By conceptually relating these ideas to Spring Boot and academic subjects, students gain a clearer understanding of how theory supports real-world security implementation.
9. Discussion Questions
1. How does reflective understanding of security concepts influence application design choices?
2. Why should authentication and authorization be treated as distinct responsibilities?
3. How do Spring-based security mechanisms reflect topics studied in BCA and MCA programs?
4. What challenges emerge when implementing security in large or distributed systems?
Course Relevance
This topic connects academic security concepts with real application behavior, helping students understand how access control is managed in enterprise systems.
It strengthens architectural thinking by encouraging learners to analyze systems beyond functional requirements.
The discussion aligns well with industry-oriented curriculum goals without relying on deep framework specialization.
Academic Concepts Covered
• Authentication and Authorization as core security principles.
• Role-based access control and permission management.
• Client–server trust and secure session handling.
Teaching Note
• Introduce concepts conceptually before tools or frameworks.
• Use familiar real-world systems to explain abstract ideas.
• Emphasize reasoning and flow over configuration memorization.
Learning Objectives
• Explain authentication and authorization using practical scenarios.
• Relate security mechanisms to BCA and MCA syllabus topics.
• Develop architectural awareness of secure system design.